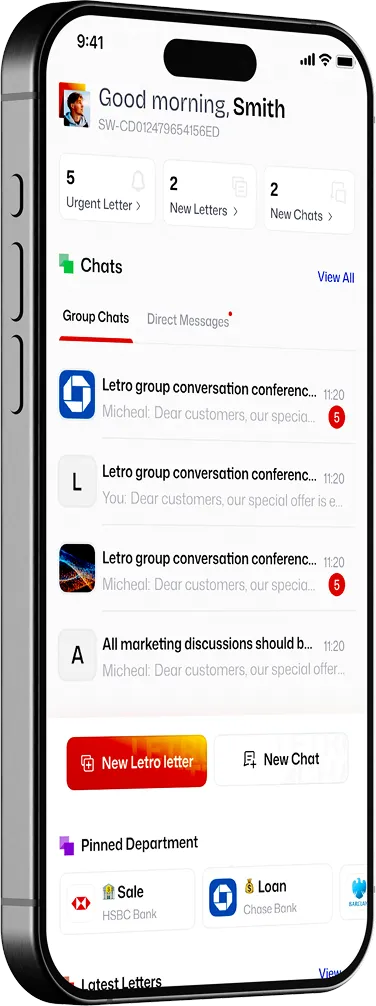
Formal communication, Rethought



Private Deployment: Simple and Fast Implementation
Run Letro in the environment that matches your security model: from controlled cloud deployments to infrastructure you manage yourself.


Data Residency and Sovereign Control
Choose where communication data lives, which jurisdiction it sits under, and how it is governed.
With decentralized federation, data will travel between private data host.


Digital Identity
Streamlines KYC with Passport Scanning and proves of identity, ensuring user individuality with PostNumber.


Interoperable Architecture (Web2 & Web3)
Storing proofs in Blockchain( Proof of letters, Identities, and actions), Integration with CRMs, ERPs, and legacy software.


Compliance: SOC2 - HIPPA - ISO27001
Enterprise-grade security, ensuring top-tier data protection and compliance
Enterprise Governance and Access Control
Security does not stop at encryption. Letro also provides organisation-aware controls for roles, approvals, and policy-driven workflows.
1. Organization-Aware Structure
Model communications around departments, legal entities, teams, and external counterparts. This makes Letro a perfect secure Slack alternative with video and voice call.
2. Role-Based Access Control
Define who can view, send, approve, escalate, or administer communications.
3. Approval and Escalation Workflows
Support templates, review steps, escalation paths, and audit-friendly process design.
4. Governance Without Breaking Security
Keep enterprise controls around the workflow while preserving end-to-end protection for message content.
Enterprise Governance and Access Control
Security does not stop at encryption. Letro also provides organisation-aware controls for roles, approvals, and policy-driven workflows.
1. Organization-Aware Structure
Model communications around departments, legal entities, teams, and external counterparts. This makes Letro a perfect secure Slack alternative with video and voice call.
2. Role-Based Access Control
Define who can view, send, approve, escalate, or administer communications.
3. Approval and Escalation Workflows
Support templates, review steps, escalation paths, and audit-friendly process design.
4. Governance Without Breaking Security
Keep enterprise controls around the workflow while preserving end-to-end protection for message content.
Deploy Letro on infrastructure dedicated to your organisation — in a private cloud, on-premise, or in isolated / air-gapped environments where higher assurance is required.
The deployment is easy, fast and affordable.
With private sovereignty, no one has access to your data and you are in control.

Post
- Slow
- Manual tracking
- Limited reach
- Some security challenges
- Bad for the environment


- Slow
- Manual tracking
- Limited reach
- Some security challenges
- Bad for the environment


Messaging Apps
- Instant
- Casual
- Lack of formality
- The mother of disturbance: Overwhelming traffic of messages
- Not connected properly to organizations



- Dedicated formal communication
- Instant: It will reach exactly to the right person
- Professional: Formal templates and tools
- Institutionally recognized
Letro is built on Matrix, an open source standard for decentralized real-time communication. That gives Letro a stronger foundation for federation, Sovereign deployment, private deployment, end-to-end encryption and interoperability — without locking communication into a single vendor-controlled system.

End-to-End Encryption by design
Matrix supports end-to-end encryption for secure one-to-one and group communication, helping protect message content from intermediary access.

Open standard foundation
Matrix provides open APIs for real-time communication, giving Letro a future-ready base for interoperability, integrations and reduced vendor lock-in over time.

Federation by design
Matrix homeservers communicate directly with each other in real time, so separate organisations can stay on separate servers and still communicate across trusted domains.

Air-gapped path for high-security environments
For higher-assurance use cases, Matrix-based deployments can also be installed in isolated and air-gapped environments with no internet connectivity.
Built for regulated communication

Healthcare & Insurance
- Sensitive communication
- Claims and case-related updates
- Protected document delivery.
Banking
- Client onboarding
- Account notices
- Approvals and Secure document exchnage
Government
- Citizen notifications
- Service applications
- Official correspondence and cross-organisation communication
Legal & Compliance
- Formal notices
- Case updates
- Document requests and controlled communication trails


The Proof is in the Protocol:
Philosophers often see identity as fluid—shaped by personal experience—while institutions treat it as fixed, anchored by documents or databases. Yet despite these contrasting views, identity has always been crucial because it determines access. Whether we’re talking about property, opportunities, or societal belonging, identity is the key that grants or denies entry.



What is a zero-knowledge proof?
One of the core principles of Web3, transparency, can also be one of its greatest drawbacks. Nobody wants all of their online activity, from financial transactions to personal identity data, to be publicly available for anyone to view. In order for blockchains to scale and become more accessible, privacy has to be a priority.



Zero-Knowledge proofs
One of the core principles of Web3, transparency, can also be one of its greatest drawbacks. Nobody wants all of their online activity, from financial transactions to personal identity data, to be publicly available for anyone to view. In order for blockchains to scale and become more accessible, privacy has to be a priority.

Discuss Your Deployment Model
Whether you need a standard rollout, private infrastructure, or stricter residency and isolation requirements, Letro gives you a trustless foundation for secure client communication.













